Constitution
Passwords, please?
You can’t make this up. Now the government is demanding your password. Passwords for e-mail, on-line backup, social networking, you name it, the government might want it. If anyone had sent in a treatment of such a concept to producer Rod Serling, during his Twilight Zone days, that might have been too far out even for him. The problem: this isn’t in a treatment. So don’t look for any “story by” line to flash up before your eyes. This is for real.
Where did this story come from?
The story, according to Declan McCullough at CNET, comes from two IT workers who have seen such government orders. To protect those sources, McCullough won’t say whom they work for. The sources tell him their companies don’t turn over those passwords just because the government asks. “Over my dead body!” sums up the usual attitude.
Which is as it should be. As McCullough points out, if the government has your e-mail password, it has your e-mail. It can read your mail before you get it. It can even send out mail in your name. Judge Andrew Napolitano, late of New Jersey Superior Court, got angry enough with the FBI for its “entrapment” cases. (Some naïve Arab kid mouths off about blowing things up in the name of jihad. The FBI then sets him up with a fake bomb, waits for him to push a dummy button, then “busts” him.) Imagine what he will say about this! With this tool, the government can ruin your reputation.
The folly of reusing a password
But the problem goes further than that. Most users reuse passwords. Composing a password is hard work, and how if you forget it? So a typical user will think of one password for e-mail, Facebook (or LinkedIn), Google, Yahoo!, Amazon.com, or whatever aggregator, merchant, or other company they have accounts with. Compromise the password at any one of these places, and a hacker now has your whole life!
Or now, the government has it.
What do the Big Boys have to say about this?
McCullough checked with the Biggest Boys on the Internet, to see whether any of them would talk for the record. Neither Microsoft nor Google would say whether the government had ever come to them asking for a user’s password. Both companies say they’d never give it.
But can we trust them? Google has a horrible track record about user’s privacy. That’s why this user, and several others, now look for alternative search engines.
And get this: Apple, Facebook, AOL, Verizon, AT&T, Time Warner Cable and Comcast would not even talk about whether they would give up your password.
McCullough failed to ask about one other kind of company: a Web host. Many activists have Web pages. ISP’s provide bare-bones Web hosting, but if you want a proper site, you need a high-powered host. CNAV asked an employee at one of the most prominent hosts, that offers various hosting plans from “shared servers” to fully dedicated servers. He replied:
We have very strict security policies in place to protect our customers, including a thorough verification process to ensure that anyone we give out information to is verified as having control of the account.
But would his company give a password to any government agent who flashed an ID? CNAV asked that. The employee emphatically denied that, and added:
In order to access information related to an account an individual would need to be fully verified on the billing account they are requesting information about.
In other words, no one gets a password from this company who is not already entitled to have it. CNAV will not reveal that company’s name, out of respect for the company’s wishes. Anyone reading this who has a Web site, should ask your host the same questions and see whether you get the same answers.
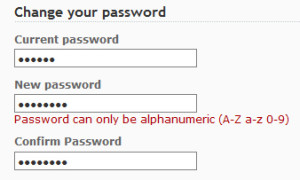
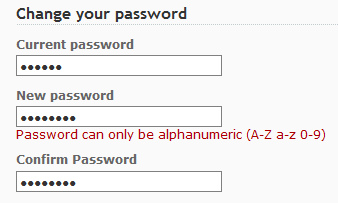
How to protect your password
For one thing, every user should look into password management. If you’re afraid you’d forget a bunch of passwords, then you want them in one place, under your control. That can be on your desktop, or other device that no one but you can get their hands on.
Because you never want to use the same password twice with different companies. That means one password for your regular Internet Service Provider, one for any third-party e-mail server, and one each for Facebook, LinkedIn, and whatever other social network or regular merchant you have.
The ideal password should have at least thirteen characters, any oneof which could be an uppercase, a lowercase, a numeral, or a common punctuation mark. If the company where you want to register does not allow that, lengthen the password to fifteen characters. Make them totally random and unpronounceable.
But don’t defeat your purpose by storing your passwords in an easily accessible form. CNAV reminds its readers of one famous case. Authorities in the Far East, about ten years ago, arrested a suspect in several cases of sabotage and mass murder. They caught him, literally, with his pants down – and with a laptop computer with a clear-text file holding every password he used. Those passwords unlocked a treasure trove of intelligence take and evidence. And the suspect’s name? Khalid Sheikh Muhammad.
Constitutional questions
McCullough called the law “murky” on the question of whether the FBI or the NSA or any other agency of the government can do this. But one part of our law is clear as crystal: the Constitution.
The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated.
A computer account is a paper within the meaning of that clause. A piece of electronic mail is certainly a paper, just as surely as a handwritten or typewritten letter is. Therefore, the government stands in direct violation with this policy.
ARVE Error: need id and provider
[subscribe2]
Terry A. Hurlbut has been a student of politics, philosophy, and science for more than 35 years. He is a graduate of Yale College and has served as a physician-level laboratory administrator in a 250-bed community hospital. He also is a serious student of the Bible, is conversant in its two primary original languages, and has followed the creation-science movement closely since 1993.
-
 Clergy5 days ago
Clergy5 days agoWhy Do The American People Let The Corrupt Media & Politicians Set The Propaganda Narrative – Speak On Their Behalf
-
![CHAPTER 10: Objective Reality Is Required for a Free Society Space Is No Longer the Final Frontier—Reality Is [upcoming release May 2024]](https://cnav.news/wp-content/uploads/2024/04/Objective-reality-v-acceptance-400x240.png)
![CHAPTER 10: Objective Reality Is Required for a Free Society Space Is No Longer the Final Frontier—Reality Is [upcoming release May 2024]](https://cnav.news/wp-content/uploads/2024/04/Objective-reality-v-acceptance-80x80.png) Education5 days ago
Education5 days agoCHAPTER 10: Objective Reality Is Required for a Free Society Space Is No Longer the Final Frontier—Reality Is [upcoming release May 2024]
-

 Human Interest4 days ago
Human Interest4 days agoIdaho prepares to defend its abortion ban
-

 Civilization3 days ago
Civilization3 days agoEarth Day Should Celebrate U.S. Progress & Innovation
-

 Education1 day ago
Education1 day ago‘Grading for Equity’: Promoting Students by Banning Grades of Zero and Leaving No Class Cut-Ups Behind
-
 Civilization2 days ago
Civilization2 days agoNewsom plays silly abortion politics
-
 Education3 days ago
Education3 days agoThe Intifada Comes to America. Now What?
-

 Civilization3 days ago
Civilization3 days agoEarth Day – part of cultural Marxism